- Automatically exporting labels when they are marked as complete.
- Setting up a daily report to track the number of annotation tasks submitted for review each day.
Setting Up Webhooks
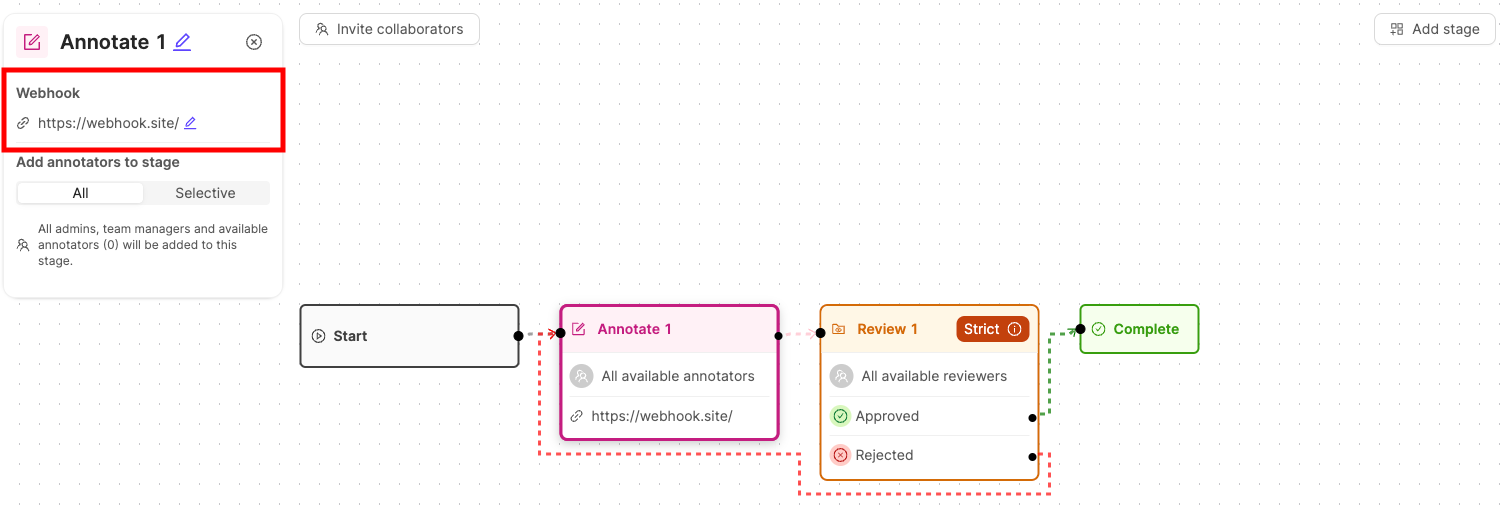
Webhooks can be set up when creating or editing a Workflow. This includes setting up a Workflow while creating a new annotation Project, creating a Workflow template, or editing the Workflow of an existing Project.Webhooks can only be added to Annotate and Complete stages. Webhooks on Annotate stages trigger when tasks are submitted for review. Webhooks on Complete stages trigger when a task is completed.
- With the Workflow open, click the Workflow stage you want to create a webhook for. A pop-up for to configure the Workflow stage appears.
- In the pop-up, click the Edit symbol under the Webhook heading.
- Enter the URL you want the JSON payload to be sent to. Press Enter on your keyboard to confirm.
- Ensure you save your changes.
After adding or updating a webhook URL, a unique signing secret is automatically generated for that webhook. This secret appears in the Signing Secret section below the URL field and can be used to verify webhook payloads.
Webhook Event Payloads
Task Submitted Payload
All task submitted events, triggered on the Annotate stage, have the following fields:| Key | Type | Description |
|---|---|---|
uid | string | Unique identifier of the event. |
version | integer | Major version number to indicate backwards incompatible versions. |
source | string | The source of the payload. Is always “Encord”. |
event_type | string | The event type. task_submitted_event is triggered on the Annotate stage. |
event_created_timestamp | string | A string of the timestamp in the ISO 8601 format. For example 2022-04-13T14:35:11.791161+00:00. |
payload | object | An object containing the Project and label information. |
project_hash | string | The unique identifier for the Project. |
data_hashes | string | The unique identifiers for the data unit. |
label_hashes | string | The unique identifiers for the Label Row. |
Task Completed Payload
All task completed events, triggered on the Complete stage, have the following fields:| Key | Type | Description |
|---|---|---|
uid | string | Unique identifier of the event. |
version | integer | Major version number to indicate backwards incompatible versions. |
source | string | The source of the payload. Is always “Encord”. |
event_type | string | The event type. task_completed_event is triggered on the Complete stage. |
event_created_timestamp | string | A string of the timestamp in the ISO 8601 format. For example 2022-04-13T14:35:11.791161+00:00. |
payload | object | An object containing the Project and label information. |
label_hash | string | The unique identifier for the Label Row. |
project_hash | string | The unique identifier for the Project. |
data_hash | string | The unique identifier for the data unit. |
Verifying Webhook Signatures
Encord signs every webhook request so you can confirm it genuinely originated from Encord and has not been tampered with.Verification is optional but recommended for production integrations.
How it works
Every webhook request includes two headers:X-Encord-Signature- an HMAC-SHA256 hex digest of the timestamp and request body, formatted as{timestamp}.{body}X-Encord-Timestamp- a Unix timestamp of when the request was sent
Retrieving your signing secret
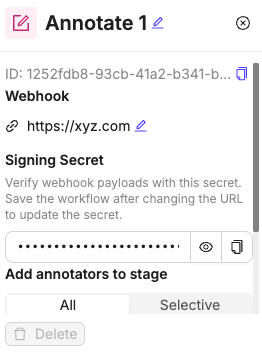
A signing secret is only generated when a valid webhook URL is entered. If you change the webhook URL, a new signing secret is generated.
Managing signing secrets
You can view and copy your signing secret in several ways:- In Workflow configuration: When setting up or editing a webhook in a Workflow stage, the signing secret appears below the URL field with options to show/hide and copy the secret.
- In webhook management: From your user settings, you can access all your webhooks and copy their signing secrets using the copy button next to each webhook entry.
Verifying the signature
To verify a request, recompute the signature on your server and compare it against theX-Encord-Signature header.
Replay protection
Use theX-Encord-Timestamp header to reject requests with a timestamp older than a reasonable threshold (for example, 5 minutes). This prevents replay attacks where a valid request is captured and re-sent.
If no signing secret is configured for a webhook URL, the
X-Encord-Signature and X-Encord-Timestamp headers are not included in the request.IP Addresses for Webhooks
For teams with advanced security practices, you must add our IP addresses to an approved list to ensure that only trusted incoming traffic from our services can reach your webhook endpoints.- Default Deployment (EMEA)
- US Deployments
34.89.106.119/3234.142.51.70/32

